
With more than 2 billion Android devices active each month, any one of them can be exploited using a remote administration tool (commonly known as a RAT). AhMyth is one of these powerful tools that can help outsiders monitor a device's location, view text messages, take camera, screenshots, and even record with a microphone without the user's knowledge.
Remote management tools are programs that provide technical support to remote computers by allowing administrators to log in and control devices directly. However, hackers quickly saw the potential of these tools and began using them for nefarious purposes. Advanced RATs are often used to remotely access and control a wide variety of devices, but today we will focus on the most popular device – Android. AhMyth is a new, open-source Android RAT, currently in development, that uses a simple GUI interface. In addition, AhMyth is also adaptable to multiple platforms, including Linux, Windows and MacOS.
The RAT consists of two parts: the first is a server-side application based on the Electron framework, in our case, our desktop or laptop, but this application can be extended to some extent if required. Acts as a control panel connected to the RAT; the second part is the client, which will be used as a backdoor to the infected Android application.
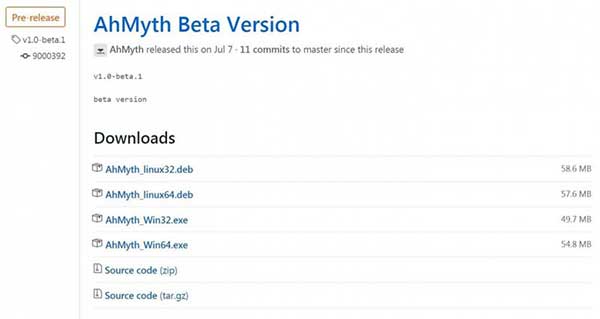
There are two ways to download and install AhMyth. Use the source directly from GitHub or use the binaries they provide.
If you choose to start from source, then you need to check that some dependencies are installed.
Java – used to generate the APK backdoor
Electron – for launching desktop applications
electron-builder and electron-packager – used to build binaries for macOS, Windows and Linux
If you have installed these, then you are ready to continue. First clone the code from GitHub using the following command.
https://github.com/AhMyth/AhMyth-Android-RAT.git
Then go to the AhMyth-Android-Rat directory below.
cd AhMyth-Android-RAT / AhMyth-Server
Once you're in, start AhMyth with the command below.
This program is still in beta development, so it's not as robust as it used to be. So it is inevitable that errors may occur during operation. If you get an error, try running it again as root as shown below.
sudo npm start --unsafe-perm
When you see the GUI start up, it means it is already working.
Source code is one way to download it, but if you're lazy like me, there's an easier way - use binaries! It's a great option when you're working on a Windows computer and don't want to mess around with the command line. But check if Java is updated on your computer.
Navigate to the AhMyth release page and download it. Currently, they only support Linux and Windows file uploads.
Download the correct file - install - run automatically.
Create an APK
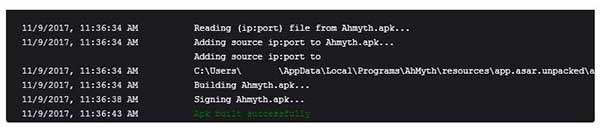
Now that we have our program up and running, it's time to build an Android application with a backdoor. At the top of the screen, select APK Builder. The first thing to change is the "Source IP", which is the IP address of the computer that will be sending and receiving the command.
For testing purposes, I'm just using my local Wi-Fi network. However, if you wish to work outside of your local network, you will need to port your computer to the Internet and use a public IP address.
AhMyth can build an APK in two different ways. It can create a standalone APK or be used to infect another app to remain hidden on the target device. To do the latter, select the box next to "Bind another app," then browse and select the APK you want to use. Today I will create the default standalone APK, but if a malicious user is deploying this APK, they will most likely bind it to another APK.
Once you have selected all the settings, you can start building the APK, just click "Build".
Find the created APK from the C:\Users\UserName\AhMyth Output\ directory

Now that you have a working APK, you can download it to the target Android device for installation. All the standard attack methods apply - anything that gets the user to download the APK. Social engineering often works best. For example, if you know the person, recommend an app to them and infect it.
If you have physical access to the phone, it only takes a few seconds to download and hide it. If you choose this method, the easy way is to save the APK to Drive and send a link to your phone. On most phones, the download should only take a second or two.
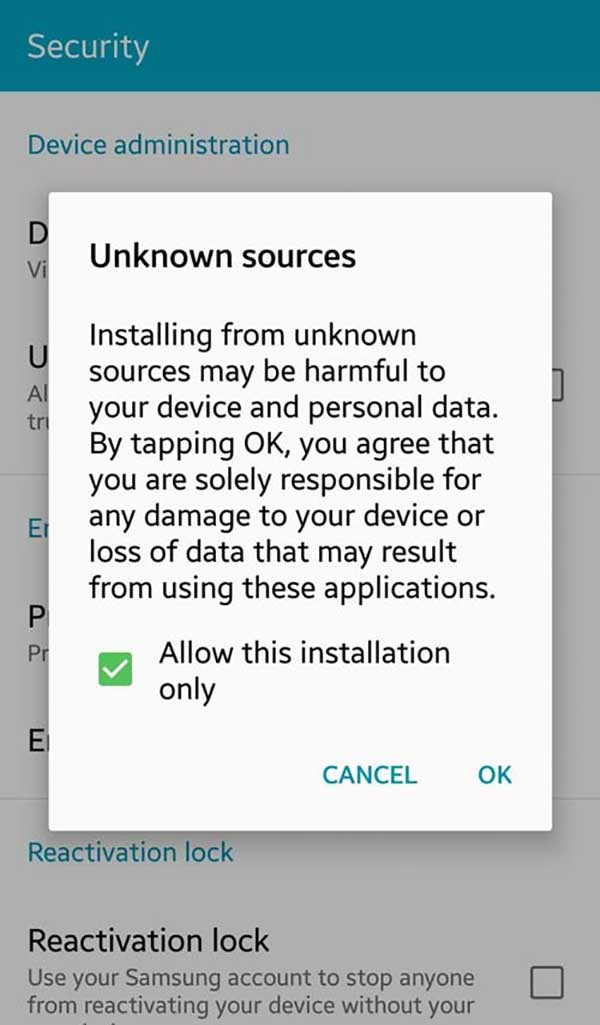
If your Android phone won't install, they probably don't have Allow "Unknown Sources" app installations enabled in their settings. Open Settings, then go to "Security" and check "Unknown Sources".
In the upper left corner of the AhMyth screen, select the Victims tab, and change the port number to the one you are using. You can also leave it empty. Next, click "Listen". Once this is done, some basic information about the monitored victim appears on the screen.

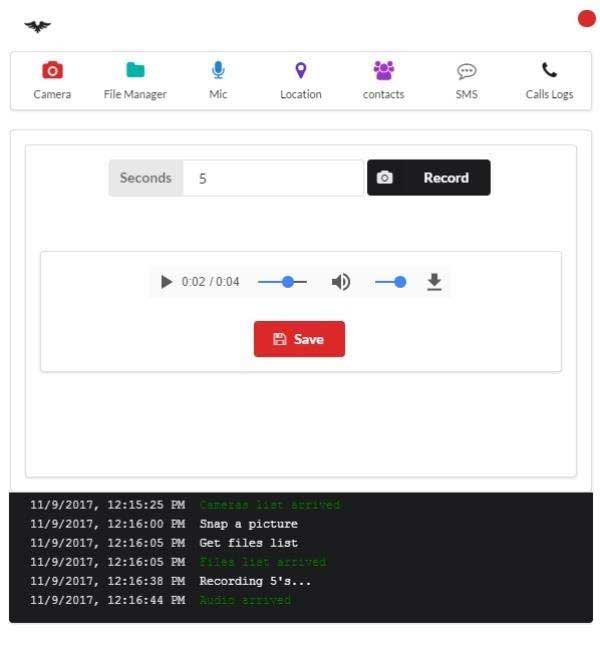
Now that you have a RAT running on the target device, you can start remote management. Click the "Open Lab" button and a new popup will appear. If you're familiar with other Android RATs like Cerberus, you might be a little disappointed with some features. The features it currently has are very powerful, such as the "file manager" function, which allows you to see everything on the device, and finding passwords, session cookies, photos, etc. is not a problem.
Another feature is the ability to record audio through the "microphone". You also have a tracking feature ("Location") where you not only know what they said but where they said it. However, one caveat is that it could be stuck with a simple GPS spoofing app.
Now you may have noticed that I skipped the "Camera" feature. It may be the reason of the old Android phone, this function does not work properly. In principle, it should allow you to send commands to take a photo with the front or rear camera and send it back to you.
In general, no one is safe from RAT attacks, but if you don't install Android apps from outside the Google Play Store, your chances of being attacked are relatively small. Installing from "unknown sources" is disabled by default in Android, but if you allow it, you greatly increase your risk because you will no longer get security prompts. If you have a legitimate reason to download APKs from outside of Google Play, be sure to click "Allow this installation only", or you may accidentally enable "Unknown Sources" permanently. Another way to protect yourself is to not take your phone to important meetings or anywhere you don't want people listening.
How to see other people's phone screen, call history, sms, conversation, text messages, email, gps location, call recording, photos, whatsapp, messenger, facebook.The mobile spy app can remotely monitor and track my partner's android phone. Download spy app for free and install apk file on target cell phone.Best spy software - Find and locate someone's phone online, read phone message from husband or wife on another cell phone.