
Nowadays mobile phones have become an indispensable part of our life. At the same time, our password has also become an important key to manage accounts, but many friends will ignore how to set a good password.
I can simply ask you a question: Do you have the habit of changing your password frequently? Not completely negative, but more than 70% of people have no habit of changing passwords, and 90% of people usually use no more than three passwords, so let me seize the first opportunity to crack the password. Because, your email password may be your App login password, and it may also be your blog password. The digital part in this password will often be your bank account password.
You can recall your password, am I wrong?
Today we will talk about the psychological technique of cracking the password. The basis for cracking the password is to first judge what type of person the other party belongs to through the observation power of the psychological technique. Different types of people set completely different passwords, based on my experience. The passwords of young people may be more complex than those of older people. Men's passwords are more complicated than women's, science students' passwords are more complicated than arts students' passwords, and almost everyone's passwords must have meaning in them. At least so far, I have never encountered a password set by the other party. A random number, so first of all, let's take a look, the rules of commonly used passwords are actually nothing more than these few rules.
This is the general password law, which is in line with the password law of most people. Usually it is composed purely of numbers, or purely of lowercase letters, or of letters plus numbers. Only a few people use underscores.

People who work hard for their careers usually have a strong sense of responsibility, and their passwords often use their own names or nicknames, or the names of their own companies.
Growing boys and girls, they pursue fashion, love to watch idol dramas, and have the habit of keeping pets. The type of password for this group of people usually uses the name or birthday of their idol, or the nickname of their pet.
People who usually have a strong sense of responsibility to their families and partners, their passwords will use the birthdays of their parents or the names of their partners and children, or their birthdays and wedding anniversaries, because these clearly reflect this type of person's love and sense of responsibility
There is a characteristic of perfectionists. These people's rooms are usually neatly arranged, and they must do it by themselves without letting other people intervene. It is almost close to obsessive-compulsive disorder. If the password of this kind of person uses the name as the password, basically he will not use the abbreviation of the name, and will definitely use the full name. If it is a word, the probability is relatively high, for example, love or beautiful. If such a person uses the date as a password, he will not say that it is 160313 in 2016. He must use the full-write format of 20160313, and he will rarely choose the form of 0313 or 160313. And they also like to use underscores. Because the underscore is usually a symmetry that can highly reflect the password. Combinations of adjectives, nouns, underscores, and numbers are often used.
When we know the combination law of the password, we only need to analyze what type of person the other party belongs to. This has narrowed the scope for us to crack the other party's password a lot.
Let's go back and talk about how I guessed the password of the other party's mobile phone. First of all, he accidentally mentioned in the chat with his agent that he will go home for dinner tomorrow, and he is so busy now that he still has to work. I often go home to see my parents. People of this type are usually very family-loving, and they belong to the family responsibility type. He hopes that his family lives within the range that he can see at any time, and he is not married, so according to experience, his password is likely to be his parents' birthday, but this is only the first guess. Because boys tend to have some Oedipus complex, most of them will use their mother's birthday as their password.
So I asked slowly, could your mother's birthday be your password? Everyone, please remember that this is an interrogative sentence, why use an interrogative sentence?
If his answer is no, then I'll try another way of guessing. But if his answer is yes, then he asks me with wide eyes how I know.
In fact, this is a screening process. Usually it's a holiday or an easy-to-remember date. For example, January 11th or February 22nd, etc., if none of the above are his passwords, then I need to continue to narrow down the range of his passwords. After I broke through his first line of defense with psychological techniques, then the next step is relatively simple, because he has completely believed that you have the ability to guess his password, and the clues he gave me are even more too much.
Then the next step is much simpler, his password must be a certain festival, and there are only a few options that are easy to guess. Of course, because other people's privacy is involved here, I can only chat with you here. In this way, is the password easier to guess than everyone thinks? Many friends may say that it takes a lot of practice to use psychological techniques, so is there an easier way?
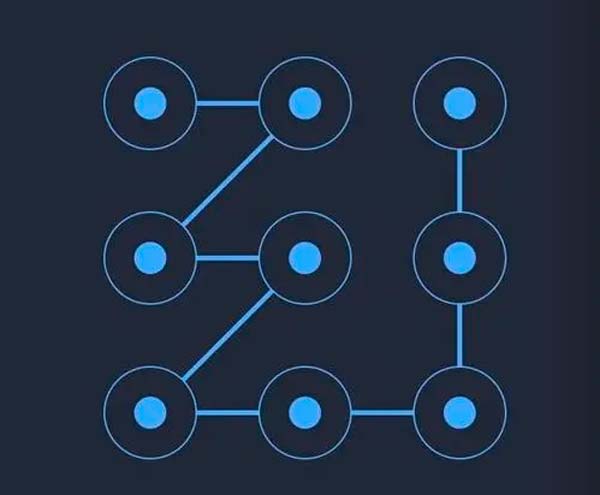
First of all, I need you to do one thing, wipe his phone screen clean. If you want to crack someone else's mobile phone password, the premise is that they don't notice it, and then remember the arrangement method of the other party's input password. The general mobile phone is 123 in the first line, then 456 in the second line, and 7890 in the third line. When the other party enters the password, you quietly peek at the curvilinear movement of his fingers, which can usually be divided into top-to-bottom, bottom-to-top, left-to-right, or right-to-left. The password entered at this time is often a continuous sequence of numbers, such as 123 or 456 or the middle 258 or 147. If there is no big change in the finger curve, it may be a repeated number or a nearby number such as 1111. The six-digit password usually adds the year, such as 820424, and the four-digit password is usually a combination of month and date, so the first number is often 0 or 1. When the other party enters 0 or 1, you can roughly confirm that he entered a date.
The last trick is why we wipe our phone screens clean. Because the other party will definitely leave fingerprints after pressing the password, when you turn off the phone screen and look at it at an angle of about 45 degrees under the light, you can easily see the fingerprints left by the other party. If you're worried that the other person's fingerprints are not obvious enough, you can buy him French fries, and his fingers will leave oil stains, which makes it easier to see the fingerprints left on the screen.
Finally, I will teach you a little trick. In addition to passwords, many websites now ask us to fill in some security questions, such as your birthday or the name of your pet. But most people confuse which question they should choose, so they usually fill in the exact same answer, which is easier to remember.