
With the development of modern technology and the enrichment of mobile phone functions, smart phones are used more and more widely in people's lives. No matter when and where, people seem to be increasingly inseparable from mobile phones. The mobile phone's functions such as surfing the Internet, shopping, taking pictures, video recording, recording, and navigation have brought great convenience to life and work, and greatly improved people's work efficiency and life pleasure.
However, while we enjoy the efficiency and convenience that mobile phones bring to work and life, mobile phones also bring us some lingering troubles. For example, data loss and accidental deletion due to human factors or mobile phone failures, or mobile phones infected with malicious viruses or implanted with Trojan horse spyware, resulting in the theft of data and account information in mobile phones, resulting in losses or personal privacy leaks, etc.
If people mistakenly delete important data and information in the mobile phone, or cannot view important data and information because they forget the password or the mobile phone is damaged, they need to delete the password and recover and extract the data from the mobile phone. If you want to fully recover and extract the important data in the mobile phone, ensure that the mobile phone will not lose data or damage the mobile phone device during the data recovery and extraction process, and avoid the leakage of the user's personal privacy, it is necessary to use professional technology to complete this work.


Cell phone spyware is similar to stalkerware in that both are able to steal data: images, videos, emails, text messages, etc., all within the control of the monitor, and they can also be obtained through regular collection lines or voIP The app eavesdrops and intercepts real-time call recordings. But cell phone spying apps generally do not target individuals, whereas cell phone tracking apps closely control a target, stealing pictures, text messages, tapping calls, and secretly recording their conversations on the Internet. Additionally, cell phone tracking apps can intercept communications from apps such as Skype, WhatsApp, and iMessage.
Like many smartphone apps, WhatsApp stores data in SQLite database files. For WhatsApp on Android devices, two databases are the most important, one is msgstore.db, which contains chat records; the other is wa.db, which contains contact lists. Dealing with these databases is relatively simple because WhatsApp has a backup function, which will backup the database to the SD card, which can be accessed without any permissions (such as root permissions). However, after installing the latest security update, the WhatsApp database is encrypted and can no longer be analyzed directly, posing a great challenge. Chat records, message records, and call records use the AES-256 standard, while media files such as photos and videos are not encrypted. And the encryption method of WhatsApp has been updated from Crypt5, Crypt7, Crypt8 to Crypt12.
So, how do we hack the WhatsApp database at this point? The most critical step is to obtain the encryption key (cipher key). When a user makes a WhatsApp backup for the first time, an encrypted key is generated, and the key is never stored in the cloud, only on the smartphone, and each smartphone corresponds to a different key. So, in order to decrypt the database, we first have to extract the encrypted key from the phone from which the backup was created. The specific path of the encryption key is: userdata/data/com.whatsapp/files/key.
Based on the research results of SalvationDATA data forensics experts, we have developed a special algorithm that can use this key file to crack the WhatsApp database. We will announce this tool soon, integrating it into the SmartPhone Forensic System (SPF), allowing users without any computer programming background to successfully crack WhatsApp's encrypted database. Users only need to import key files and encrypted database files, and the program can automatically generate correct unencrypted database files.
However, if the device is not rooted, it will not be smooth sailing to obtain the key file. So, let's discuss how to bypass WhatsApp's encryption and how to extract WhatsApp data without having root access.
key files are always stored in the WhatsApp directory along with the unencrypted database. If access to these files is available, it would be possible to view the WhatsApp communication history on the current device. The only problem is that we cannot directly access these files without root privileges.
The first method is to use the backup and restore function of the Android system. Many Android phone manufacturers allow users to create backups using built-in system apps. Backups created this way are stored on the SD card without encryption. Therefore, law enforcement can use this simple method to access WhatsApp communication records.
We can use smartphones to create WhatsApp backups. Users can find the "Backup Restore" application in the Tools folder, create a new backup, and remember to check WhatsApp. Then, we can find the WhatsApp backup data on the SD card of the phone. This backup includes all unencrypted database files and WhatsApp key files. Now, all we have to do is analyze the target database using mobile forensics tools.
Another way is to downgrade the WhatsApp app to a version that doesn't have encryption. WhatsApp version 2.11.431 was the last version that did not enforce encrypted backups. Therefore, we can downgrade WhatsApp to version v.2.11.431 without deleting user data, then use the old version of WhatsApp to create a backup file, and then extract the required database. This process requires user expertise and comes with the risk of permanent data loss. Therefore, we strongly recommend users to use professional forensic tools for version downgrade.
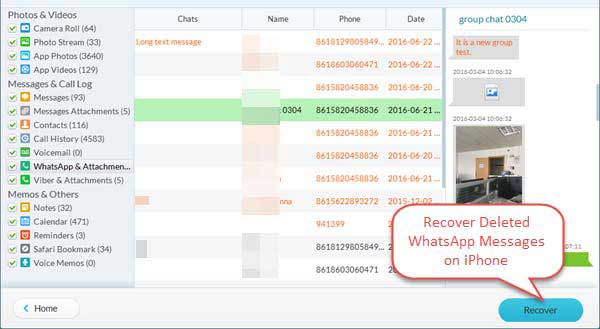
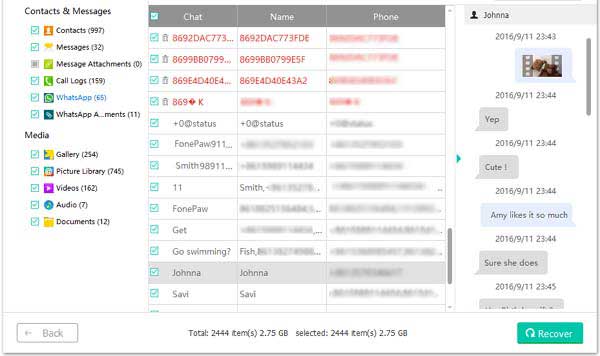
Now that we know how to extract WhatsApp database files from smartphones, let's see how to use database files to recover deleted WhatsApp messages on Android and iOS devices. There are two ways a user can delete WhatsApp messages. Users can delete messages one by one, or use the "clear/delete" chat button to delete all messages at once. According to our test results, no matter which method the user uses to delete the message, we can use the following method to restore it.
As we mentioned earlier, WhatsApp uses an SQLite database to store messages. Unlike the Android system, the iOS system will store all WhatsApp-related data in the ChatStorage.sqlite database. These database files are usually accompanied by cache files with the suffix "-wal". Most of the time, these cache files have a size of 0, but if they are not, they may contain important data that has not been stored in the database. Once this happens, we must deal with it carefully, because if we don't care about these cache files, the information stored in them may be overwritten and can never be retrieved.
According to our analysis, the WhatsApp messages that can be accessed normally are stored in msgstore.db, and the deleted messages are stored in msgstore.db-wal, which is the message cache file. WhatsApp always stores messages in a cache file before saving them in the real database. Interestingly, sometimes the cache file will be larger than the database file. This is because a message can only be stored as a single record in the database, but there is no such limitation in the cache file. A message may have multiple records at the same time. Therefore, we have a chance to recover deleted or lost WhatsApp messages.
However, to avoid overwriting data already in the cache file, we cannot directly open the database file until the cache file is properly processed. We have to process the cache file first, match the features, then save and analyze all the data in the cache file.
Take "this is a test message" as an example. When the user deletes this message, the record corresponding to the message is usually also deleted from msgstore.db. However, there may still be some records of this message in the msgstore.db-wal cache file. The situation before and after the message "This is a test message" is deleted is shown in the figure below. We can see that when the message is deleted, the relevant data is still stored in the cache file, and the offset position of the record remains unchanged.
Therefore, by analyzing and extracting data from the msgstore.db-wal cache file, we propose a way to recover deleted or lost WhatsApp messages. This aforementioned method can effectively and reliably extract deleted WhatsApp data and is also a perfect solution for recovering deleted messages and emptied chat history.
How to see other people's phone screen, call history, sms, conversation, text messages, email, gps location, call recording, photos, whatsapp, messenger, facebook.The mobile spy app can remotely monitor and track my partner's android phone. Download spy app for free and install apk file on target cell phone.Best spy software - Find and locate someone's phone online, read phone message from husband or wife on another cell phone.